The Need for Obfuscation
Obfuscation plays a vital role in software protection by making the code harder to understand, analyze, and reverse engineer. It involves transforming the code, making it difficult for attackers to extract meaningful information. Obfuscation techniques include code obfuscation, data obfuscation, and control flow obfuscation, among others. These techniques introduce complexity and confusion into the code, making it challenging for attackers to comprehend the logic and purpose of the software.
Read on Best Computer Science Assignment Help
Real-World Application of Obfuscation
Several software protection tools and libraries incorporate obfuscation techniques:
- ProGuard (Java, Android): Reduces, shrinks, and obfuscates Java bytecode.
- ConfuserEx (.NET applications): Encrypts and obfuscates .NET assemblies to prevent decompilation.
- Obfuscator-LLVM (C, C++): A low-level obfuscation tool that integrates with the LLVM compiler framework.
- JavaScript Obfuscator: Protects web-based JavaScript code from being copied or modified by unauthorized users.
According to a study published in IEEE Transactions on Information Forensics and Security, obfuscation techniques have effectively deterred reverse engineering attempts by increasing the computational effort required to decompile software.
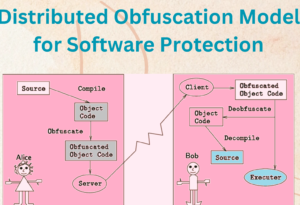
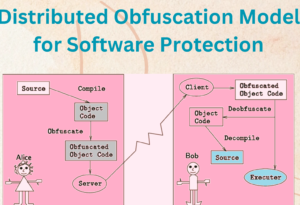
How Distributed Obfuscation Works
The working principle of distributed obfuscation follows these steps:
- Code Segmentation: The original code is split into smaller segments to be processed separately.
- Task Distribution: Each code segment is assigned to different nodes that perform individual obfuscation tasks.
- Obfuscation Process: Nodes apply various obfuscation techniques, making each segment more challenging to analyze.
- Code Reassembly: The obfuscated segments are recompiled to form the final software package.
- Deployment: The obfuscated software is deployed, increasing resistance to reverse engineering and unauthorized access.
- Runtime Protection: To prevent live analysis, additional security measures, such as anti-debugging mechanisms, are integrated into the final software.
Benefits of Distributed Obfuscation
Implementing a distributed obfuscation model offers several benefits:
- Enhanced Security: Distributed obfuscation adds a layer of complexity and confusion to the software, making it significantly harder for attackers to reverse engineer or understand the code.
- Improved Scalability: By leveraging distributed systems, the obfuscation process can be parallelized and scaled to handle large software applications effectively.
- Resource Utilization: Distributing the obfuscation tasks among multiple nodes ensures efficient utilization of computing resources and reduces the time required for obfuscation.
- Resilience to Attacks: The obfuscation process’s distributed nature makes it more resilient to attacks, as compromising a single node does not reveal the complete obfuscation logic.
- Future-proofing: As computing power advances, distributed obfuscation models can adapt and leverage the increased resources, ensuring the effectiveness of software protection mechanisms.
Sample Draft Paper
Advantages of Distributed Obfuscation
1. Enhanced Security
By distributing the obfuscation process across multiple machines, attackers face more significant challenges in reconstructing the original logic.
2. Scalability and Efficiency
The distributed model enables parallel processing, reducing obfuscation time for large software applications.
3. Better Resource Utilization
Obfuscation workloads are shared across multiple nodes, making better use of available computing power.
4. Resilience to Attacks
A compromised node does not reveal the complete obfuscation logic, ensuring higher security against targeted attacks.
5. Future-Proofing
Distributed obfuscation can scale to maintain robust security protections as computing power advances.
Challenges and Limitations of Distributed Obfuscation
1. Increased Complexity
Managing task distribution, synchronization, and node communication requires advanced infrastructure and expertise.
2. High Resource Demands
Large-scale distributed obfuscation may require substantial computational resources, making it more expensive.
3. Potential Overhead and Latency
Network communication between nodes may introduce latency, impacting performance.
4. Maintenance and Updates
Keeping a distributed obfuscation system up-to-date requires ongoing monitoring and fine-tuning.
Future Implications and Potential Applications
The distributed obfuscation model holds promising implications for the future of software protection. Distributed obfuscation can become integral to software development practices as computing power and cloud technologies advance. It has the potential to protect sensitive algorithms, intellectual property, and valuable trade secrets across various domains, including:
- Mobile Applications: Protecting mobile applications against reverse engineering and unauthorized access.
- IoT Devices: Safeguarding the firmware and software running on Internet of Things (IoT) devices from tampering and exploitation.
- Cloud-based Software: Ensuring the security and integrity of software deployed on cloud platforms.
- Digital Rights Management: Preventing unauthorized copying, distribution, and modification of copyrighted software.
Conclusion
The distributed obfuscation model offers a robust and effective solution for software protection in the face of evolving threats. By leveraging distributed systems and cloud computing, software developers can enhance the security and integrity of their applications. Distributed obfuscation adds complexity, confusion, and resilience to reverse engineering attempts, making it significantly harder for attackers to compromise the software. As technology advances, distributed obfuscation is poised to become essential to software protection strategies, providing a shield against unauthorized access and intellectual property theft.
FAQs








 Evan John
Evan John