A perfect academic essay requires careful planning, research, and attention to detail. It is essential to follow a structured approach and adhere to the guidelines provided by your instructor or academic institution. Following the steps outlined in this guide, you can create a well-written essay showcasing your knowledge and analytical skills.
What Is an Academic Essay?
An academic essay is a formal piece of writing that presents a well-structured argument or analysis on a specific topic. It assesses a student’s understanding, research skills, and communication ability. The essay includes an introduction with a thesis statement, body paragraphs with supporting evidence, and a conclusion summarising the main points. Academic essays require a formal tone, logical structure, and proper citations. They demonstrate critical thinking, engagement with relevant literature, and the ability to draw well-supported conclusions. Academic essays are essential for showcasing knowledge and analytical skills and contributing to scholarly discourse.
Read more on Informative Essay Topics for All Students
Types of Academic Essays
Students encounter several types of academic essays during their educational journey. Each type serves a distinct purpose and requires specific approaches to writing. Here are some common types of academic essays:
- Expository Essay: This type of essay aims to explain or describe a concept, idea, or process clearly and objectively. It presents information, facts, and evidence to inform readers about a particular topic.
- Argumentative Essay: In an argumentative essay, the writer presents a specific claim or viewpoint on a controversial issue and provides evidence and reasoning to support it. The goal is to persuade the reader to accept the writer’s perspective.
- Persuasive Essay: Similar to argumentative, a compelling essay seeks to convince the reader to adopt the writer’s position on a particular topic. It employs emotional appeals, logical arguments, and rhetorical devices to sway the reader’s opinion.
- Descriptive Essay: An explanatory essay vividly portrays a person, place, object, or event using sensory details. It aims to create a vivid and engaging picture in the reader’s mind.
- Narrative Essay: A narrative essay tells a story or recounts a personal experience. It often includes elements such as characters, setting, plot, and dialogue to engage the reader.
- Compare-and-contrast essay: This type of essay explores the similarities and differences between two or more subjects. It examines their characteristics, qualities, and relationships to provide insights into the compared topics.
- Cause and Effect Essay: A cause and effect essay analyzes the causes and consequences of a particular event, phenomenon, or situation. It explores the reasons behind an occurrence and the outcomes that result from it.
- Analytical Essay: An analytical essay thoroughly examines and interprets a text, idea, or piece of literature. It requires breaking down the subject into its constituent parts, analyzing its components, and presenting an evaluation or critique.
- Research Essay: A research essay involves extensive research on a specific topic and presenting a well-supported argument or analysis based on scholarly sources. It requires proper citation and referencing of the researched materials.
These are just a few examples of the types of academic essays students may encounter. Each type has its structure, approach, and style requirements. Understanding the purpose and expectations of each essay type is crucial for producing compelling and well-written academic writing.
Structure of an Academic Essay
A well-written academic essay typically consists of three main parts
-
Introduction – This section provides background information on the topic and includes a thesis statement, which outlines the central argument or focus of the essay. A strong introduction captures the reader’s interest and sets the stage for the discussion.
-
Body Paragraphs – The essay’s body is divided into multiple paragraphs, each presenting a clear argument or supporting point. These paragraphs should follow a logical sequence and include evidence from credible sources, such as academic journals, books, or expert opinions. Proper use of citations (APA, MLA, or Chicago style) strengthens the argument’s credibility.
-
Conclusion – The conclusion summarizes the key points discussed in the essay and reinforces the thesis statement. It should not introduce new information but rather provide a final reflection or implication of the argument.
Why Are Academic Essays Important?
Academic essays develop key skills such as:
-
Critical Thinking – Encouraging analysis and evaluation of different perspectives.
-
Research Proficiency – Enhancing the ability to gather and assess credible sources.
-
Communication Skills – Improving clarity and coherence in writing.
Professors and researchers use essays to contribute to scholarly discourse, ensuring ideas are presented in a structured and logical manner.
Academic Essay Sample
There are different essays. Below is a sample of an academic essay:
1. Influence of Social Media On Music Artist Management- Argumentative Essay
2. Graph organizer s1 12.01.21
Best Practices for Writing an Academic Essay
To write an effective academic essay, consider the following tips:
-
Develop a Clear Thesis – Ensure your argument is well-defined and specific.
-
Use Credible Sources – Reference peer-reviewed articles, books, and expert insights.
-
Maintain a Formal Tone – Avoid slang, contractions, or overly casual language.
-
Follow a Logical Structure – Use clear topic sentences and transition words.
-
Cite Sources Properly – Use the appropriate citation style (APA, MLA, etc.) to avoid plagiarism.
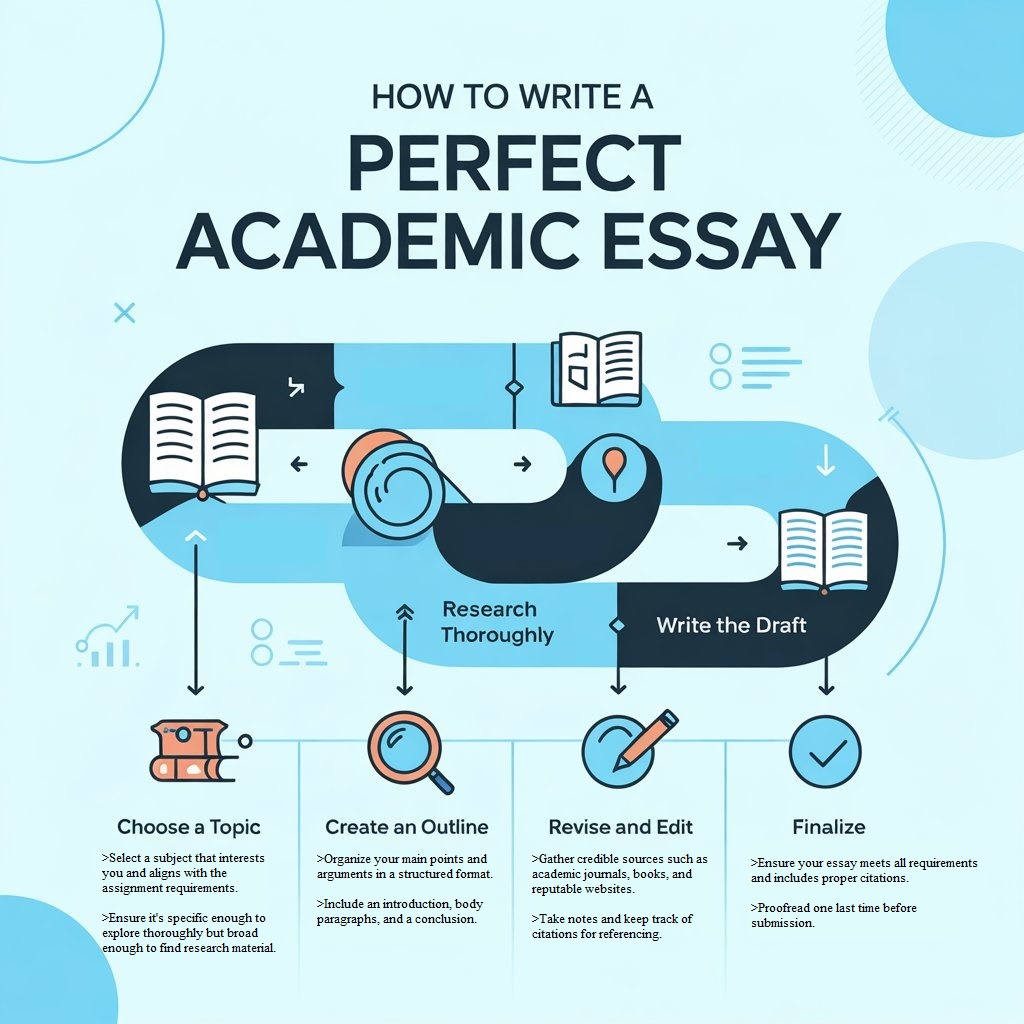
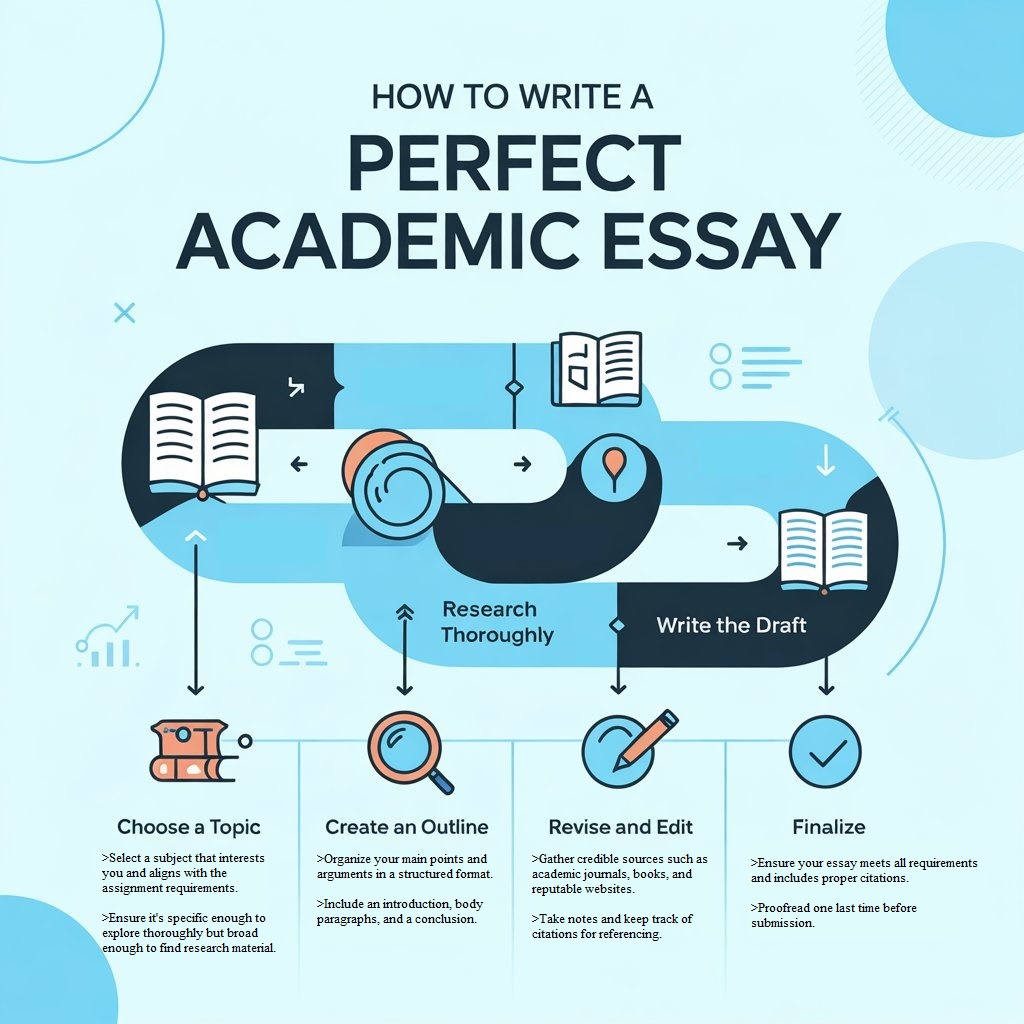
Academic Essay Process
Understand the Essay Prompt
The first step in writing a perfect academic essay is thoroughly understanding the prompt. Read the prompt carefully and identify the key requirements and instructions. Pay attention to the topic, word count, formatting guidelines, and specific research or citation requirements. A clear understanding of the prompt will help you stay focused and ensure that your essay addresses the given topic effectively.
Conduct Thorough Research
Once you clearly understand the essay prompt, thoroughly research the topic. Gather relevant information from reliable sources such as academic journals, books, reputable websites, and scholarly databases. Take detailed notes and organize the information based on its relevance to your essay. Ensure that you cite all your sources properly to avoid plagiarism.
Develop a Strong Thesis Statement
A strong thesis statement is the foundation of a well-written academic essay. It presents the central argument or idea that your essay will explore and support. Your thesis statement should be clear, concise, and specific. It should also be arguable and provide a roadmap for the rest of your essay.
Create an Outline
Before you start writing, create a comprehensive outline that will serve as a roadmap for your essay. An outline helps you organize your thoughts and ensures your essay flows logically. Divide your essay into sections and subsections, assigning headings and subheadings to each. This will help you maintain a clear structure and make your essay easier to read.
Read on How to write like DR Seuss
Write the Introduction
The introduction is your opportunity to grab the reader’s attention and introduce your topic. Start with a compelling opening sentence that hooks the reader and provides context for your essay. Provide background information and gradually narrow down to your thesis statement. The introduction should be concise but informative, setting the tone for the rest of your essay.
Write Well-Structured Body Paragraphs
The body paragraphs of your academic essay should expand on the main points presented in your thesis statement. Each paragraph should focus on an idea or argument and provide supporting evidence or examples. Start each paragraph with a topic sentence introducing the main point, followed by supporting sentences and relevant evidence. Ensure smooth transitions between paragraphs to maintain a coherent flow of ideas.
Use Proper Citation and Referencing
When incorporating information from your research, it is crucial to use proper citation and referencing. Follow the citation style specified by your instructor, such as APA, MLA, or Chicago. Include in-text citations for direct quotes, paraphrases, and information that is not common knowledge. Create a reference list or bibliography at the end of your essay to acknowledge all the sources you have used.
Write a Compelling Conclusion
The conclusion of your academic essay should summarize your main points and restate your thesis statement. It should leave a lasting impression on the reader and provide a sense of closure. Avoid introducing new information in the conclusion and focus on reinforcing your main arguments. End with a thought-provoking statement or a call to action related to your essay’s topic.
Revise and Edit
After completing the initial draft of your essay, take the time to revise and edit it. Review the content for clarity, coherence, and logical flow. Ensure each paragraph contributes to the overall argument and supports your thesis statement. Eliminate any repetitive or irrelevant information. Check for grammar, punctuation, and spelling errors.
Proofread for Grammar and Spelling Errors
Proofreading is a crucial step in the essay writing process. Carefully read through your essay, paying attention to grammar and spelling errors. Use grammar-checking tools or seek assistance from a proofreader if needed. Correct typos, punctuation, or grammatical errors to ensure your essay is error-free and polished.
Seek Feedback
Seek feedback from peers, professors, or writing tutors. Their insights and suggestions can help you improve your essay’s clarity, structure, and overall quality. Consider their feedback objectively and make necessary revisions to strengthen your arguments and address weaknesses.
Finalize Your Essay
Incorporate the feedback received and make the final revisions to your essay. Ensure the document’s formatting, citation style, and referencing are consistent. Proofread one last time to catch any remaining errors or inconsistencies.
Conclusion
A perfect academic essay requires careful planning, research, and attention to detail. By following a systematic approach, understanding the essay prompt, conducting thorough research, and writing well-structured paragraphs, you can create an essay that effectively communicates your ideas and impresses your readers. Remember to revise, edit, and proofread your essay to ensure it meets the highest standards of academic writing.
Best Practices for Writing an Academic Essay
A strong academic essay requires careful planning, research, and attention to structure. Below are key best practices to follow:
1. Develop a Clear Thesis
The thesis statement is the foundation of your essay. It should clearly state your main argument or purpose concisely and precisely. A strong thesis:
-
Takes a clear stance or position on the topic.
-
It is debatable, inviting discussion rather than stating an obvious fact.
-
Guides the direction of your essay, ensuring each body paragraph supports your argument.
For example, instead of writing a vague thesis like:
“Climate change affects the environment,”
a more substantial thesis would be:
“Climate change is accelerating coastal erosion, leading to significant economic and ecological consequences that require immediate policy intervention.”
2. Use Credible Sources
Academic essays require well-researched, reliable evidence to support claims. Using low-quality or biased sources weakens your argument. When selecting sources, consider:
-
Peer-reviewed journal articles – These have undergone rigorous evaluation by experts.
-
Academic books – Scholarly texts written by subject-matter experts.
-
Government and institutional reports – Reliable data from research organizations or agencies (e.g., World Health Organization, United Nations).
-
Primary sources – Firsthand accounts such as interviews, historical documents, or case studies.
Avoid relying on Wikipedia, opinion blogs, or unverified websites unless they cite authoritative sources.
3. Maintain a Formal Tone
Academic writing should be professional and objective. To achieve this:
-
Avoid slang and contractions: Use “do not” instead of “don’t” and “cannot” instead of “can’t.”
-
Use precise language: Instead of “a lot of,” say “numerous” or “a significant amount.”
-
Stay neutral: Do not use personal opinions unless required. Instead of “I think this policy is unfair,” say, “This policy disproportionately affects marginalized communities, as evidenced by [source].”
A formal tone enhances credibility and ensures your writing aligns with academic standards.
4. Follow a Logical Structure
A well-structured essay enhances readability and argument flow. Keep these key elements in mind:
-
Introduction: Start with a hook (a thought-provoking statement, statistic, or question) and introduce the topic before stating your thesis.
-
Body Paragraphs: Each paragraph should focus on one main point that supports the thesis. Use topic sentences, evidence, and analysis.
-
Transitions: Smoothly connect ideas using words like “furthermore,” “in contrast,” and “therefore.”
-
Conclusion: Restate the thesis, summarize key points, and provide a final thought or implication.
5. Cite Sources Properly
Proper citation not only avoids plagiarism but also strengthens your credibility. Different fields require different citation styles, such as:
-
APA (American Psychological Association): Used in psychology, education, and social sciences.
-
MLA (Modern Language Association): Common in humanities and literature.
-
Chicago/Turabian: Used in history and some social sciences.
Academic Essay Outline Sample

Academic Essay Sample Topics
- The Impact of Social Media on Interpersonal Communication Skills
- The Role of Education in Promoting Sustainable Development
- The Effects of Climate Change on Global Food Security
- The Influence of Advertising on Consumer Behavior
- The Ethics of Genetic Engineering in Humans
- The Implications of Artificial Intelligence on Employment
- The Relationship Between Mental Health and Academic Performance
- The Importance of Cultural Diversity in the Workplace
- The Role of Women in STEM Fields and Closing the Gender Gap
- The Impact of Globalization on Cultural Identity
Conclusion
A perfect academic essay requires careful planning, thorough research, and effective communication. You can create a well-structured essay by understanding the essay prompt, developing a strong thesis statement, organizing your ideas, and providing supporting evidence.
Remember to use proper citation and referencing, engage your readers with a conversational tone, and revise and proofread your work for clarity and accuracy. Seeking feedback from others can also help improve your essay.
Writing a perfect academic essay is an ongoing process that involves continuous learning and improvement. Embrace the challenge, invest time in developing your writing skills, and strive for excellence in your academic pursuits.








 Evan John
Evan John